The following reports enable you to visualize the overall performance of a system in the Uptime Infrastructure Monitor environment, as well as analyze the information to determine the cause of problems with those systems:
Resource Usage Report
The Resource Usage report tracks the usage of system resources and performance information for systems over a given period of time. In addition to the usage information reported on, the report displays the following information:
- the name and description of the system
- an overview of the system configuration, including architecture, memory size, operating system version, number of CPUs, and host ID
Creating a Resource Usage Report
To create a Resource Usage report, do the following:
- In the Reports Tree panel, click Resource Usage.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- Select one or more of the following report options:
- Resource Utilization
The average and maximum amount of CPU and memory use. - CPU Performance Graph
Tracks the performance of a system’s CPU over a specified time period. This information appears as a graph in the report. Multi-CPU
The percentage of total CPU time used on systems with more than one CPU.If you find the report’s rendered graph too dense due to a large number of CPUs, alternatively generate a Multi-CPU Usage graph while including fewer CPUs.
- Network I/O
The average amount of traffic, measured in megabytes per second, that is traveling through the network interfaces. The report also identifies bursts in network activity that may occur over short intervals. This information appears as a graph in the report. - Network Errors
Any errors that have occurred with the physical network interface. The errors can be, for example, collisions or handshake errors between a system and a switch. - TCP Retransmits
Any network services that may not be completing properly because of undue network or system load. This information appears as a graph in the report. - Free Memory
The amount of free memory available to the system. This information appears as a graph in the report. - Page Scanning Statistics
The number of file system pages scanned by the page scanning daemon. This information appears as a graph in the report. - Disk Statistics
The following statistics for each disk on a system:- percentage of the disk that is busy
- average queue length
- number of reads and writes per second
- number of blocks accessed per second
- average wait time, in seconds
- average service time, in seconds
If the system for which you are creating a report for has multiple disks, a graph for each disk on the system is generated.
- File System Capacity
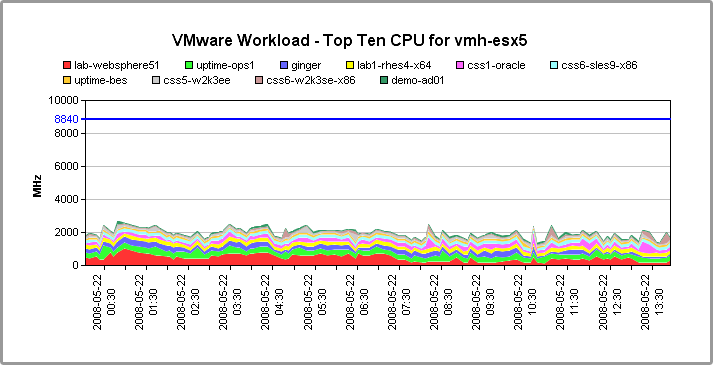
The amount of free disk space on the system. This information appears as a graph in the report. Workload (Top 10 - CPU)
The top 10 processes that are consuming CPU time, grouped by user ID, group ID, and process name. This information appears as a graph in the report.This graph does not appear when you generate this report for a VMware ESX system.
Workload (Top 10 - Memsize)
The top 10 processes that consume system memory, based on the total memory size of the processes - including virtual pages and shared memory. This information appears as a graph in the report.This graph does not appear when you generate this report for a VMware ESX system.
Workload (Top 10 - RSS)
The top 10 processes that are consuming physical memory (in KB), as measured by the run-set size (RSS) of the process. This information appears as a graph in the report.This graph does not appear when you generate this report for a VMware ESX system.
Network Device Interfaces
The Resource Usage statistics for all Network Device interfaces associated with the selected Elements. The following statistics are included:Port Name the name of the port Type the type of port Usage the percentage of the port's maximum throughput that was used by inbound and outbound packets In Rate the average throughput of inbound packets, in Mbps In Usage the percentage of the port's maximum throughput that was used by inbound packets Out Rate the average throughput of outbound packets, in Mbps Out Usage % the percentage of the port’s maximum throughput that was used by outbound packets Errors #/sec the average number of errors per second Discards #/sec the average number of packets discarded per second Status the port status Multiple historical graphs are provided for this report including:
- Total Rate (Mbps)
- Usage (%)
- In Rate (Mbps)
- In Usage (%)
- Out Rate (Mbps)
- Out Usage (%)
- Resource Utilization
- If you selected more than one report option and plan to report on more than one system, you can optionally click the Group report options by system checkbox.
Selecting this option combines the metrics for each system for which you are generating the report. - To generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems, select the systems from the List of Systems.
- Select a report generation option. See Report Generation Options for details.
- If you want to save the report or schedule it to run at a specific time or interval, complete the settings in the Save Reports section of the subpanel.
See Saving Reports and Scheduling Reports for more information.
Resource Hot Spot Report
The Resource Hot Spot report is a key checkpoint report that allows you to quickly identify servers and network devices across your enterprise that may be having performance issues, so you can immediately start working to identify what may be causing them.
The Resource Hot Spot report helps you answer the following types of questions:
- Which servers and network devices in my infrastructure were the top consumers in various resource usage categories?
- Which servers are running short on memory, or are overworked?
- Which VMs' processes need to be shared with another instance?
- Are all network devices correctly configured?
- For resource-strained Elements, is there a configuration issue or is it a resourcing issue?
The report is also a valuable investigative tool that helps you quickly focus on the parts of your infrastructure that require troubleshooting. The report can be configured to include full listings of threshold-violating servers and network devices based on key resource-usage metrics such as memory and CPU usage, port throughput caps, or packet-issue counts. The high, low, and average for these metrics are presented, along with historical graphs for offending metrics; these details can help you confirm whether sustained resource strain, or wild swings are caused by resourcing deficits or configuration errors.
The Resource Hot Spot report is also a key starter report, as it is automatically created and saved for new Uptime Infrastructure Monitor installations. This report provides a summary of top resource users for the week. By default, a PDF version of the report is emailed to the SysAdmin user group.
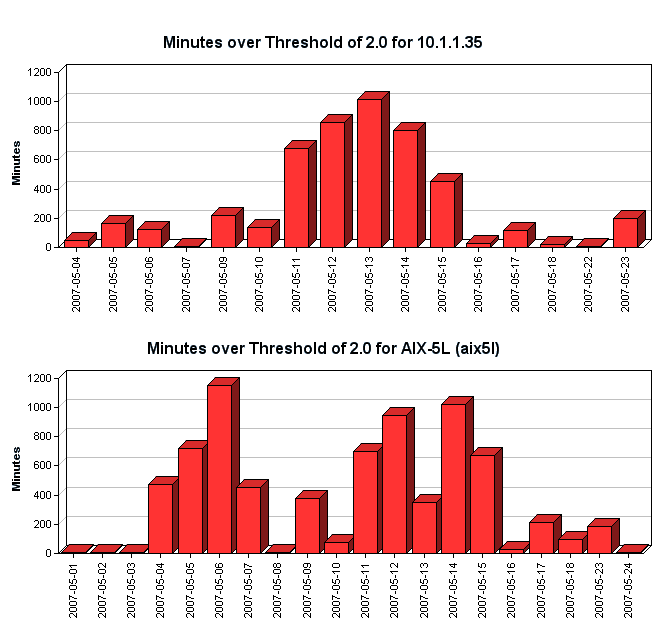
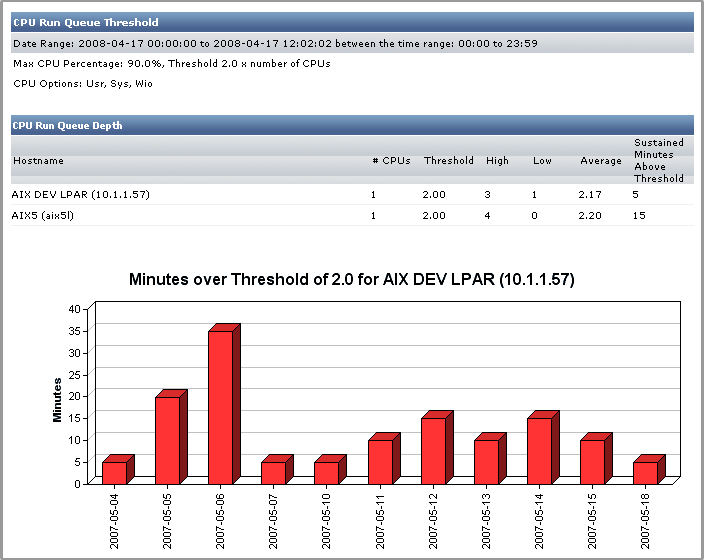
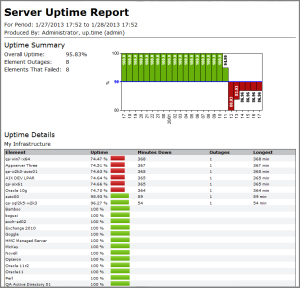
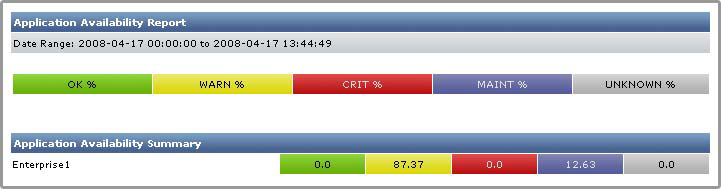
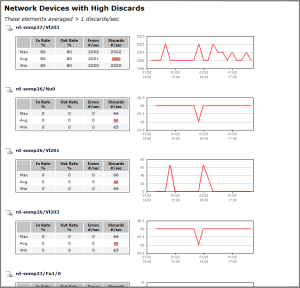
The following are portions of an example Resource Hot Spot report:
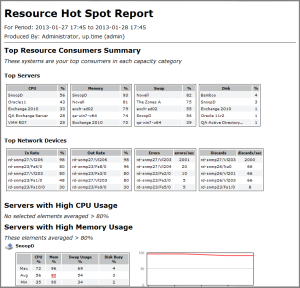
The Resource Hot Spot report is a default report that is automatically created and saved for weekly generation on new Uptime Infrastructure Monitor installations, beginning the third day after Uptime Infrastructure Monitor was first installed. |
Resource Hot Spot Report Details
The following information comprises the Resource Hot Spot report:
| Servers | |
|---|---|
| Top Servers | Of the servers included in the report, the top five resource consuming servers in terms of CPU, memory, swap usage, and disk usage. These servers are listed regardless of whether they violated resource usage thresholds set during report configuration; if your entire infrastructure is meeting your resource usage criteria for the report, the top-five servers are still included in the summary for each category. |
| CPU | The percentage of CPU capacity used during the defined time period. In the Top Servers summary, this is an average value for the time period. |
| Mem | The percentage of memory used by processes for the defined time period. In the Top Servers summary, this is an average value for the time period. |
| Swap Usage | The percentage of memory swap space used during the defined time period. In the Top Servers summary, this is an average value for the time period. |
| Disk Busy | The percentage of time the server disk is handling transactions in progress for the defined time period. In the Top Servers summary, this is an average value for the time period. |
| Servers with High CPU Usage | A listing of all servers included in the report whose average CPU usage for the time period exceeded the threshold defined during report configuration. Each server's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Servers with High Memory Usage | A listing of all servers included in the report whose average memory usage for the time period exceeded the threshold defined during report configuration. Each server's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Servers with High Swap Usage | A listing of all servers included in the report whose average memory swap space usage for the time period exceeded the threshold defined during report configuration. Each server's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Servers with High Disk Busy | A listing of all servers included in the report whose average disk processing for the time period exceeded the threshold defined during report configuration. Each server's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Network Devices | |
| Top Network Devices | Of the network-device type Elements included in the report, the five most inefficient network devices in terms of in rate, out rate, error count, and discards. These network devices are listed regardless of whether they violated throughput or error thresholds set during report configuration; if all of your network devices are passing the criteria for the report, the top-five network devices are still included in the summary for each category. |
| In Rate % | The percentage of the network device's maximum throughput, on a per port basis, that was used by inbound packets during the defined time period. |
| Out Rate % | The percentage of the network device's maximum throughput, on a per port basis, that was used by outbound packets during the defined time period. |
| Errors per sec | The average number of errors encountered per second, on a per port basis, during the defined time period. |
| Discards per sec | The average number of packets discarded per second, on a per port basis, during the defined time period. |
| Network Devices with High In Rate | A listing of all network devices included in the report whose average in-rate percentage for the time period exceeded the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Network Devices with High Out Rate | A listing of all network devices included in the report whose average out-rate percentage for the time period exceeded the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Network Devices with High Errors | A listing of all network devices included in the report whose average error-per-second count for the time period exceeded the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the violating metric with other metrics or events:
|
| Network Devices with High Discards | A listing of all network devices included in the report whose average discarded-packet count for the time period exceeded the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the violating metric with other metrics or events:
|
Creating a Resource Hot Spot Report
To create a Resource Hot Spot report, do the following:
- On the Reports tab, click Resource Hot Spot, which is found in the Performance and Analysis section of the reports tree panel.
- In the date and time range section, select a reporting window.
For more information, see Understanding Dates and Times. - In the Report Options section, configure which components comprise your report:
- top-five lists for servers or network devices in various resource-usage categories
- comprehensive lists of Elements that are experiencing performance issues in various resource-usage categories
- for the Element list, the threshold used to determine which are experiencing performance issues
- Determine which Elements are included in the resource hot-spot assessment by selecting Infrastructure Groups, Element Views, or individual Elements from the following sections:
- List of Groups
- List of Views
- List of Elements
- Continue with the desired report generation process:
- generate a report immediately to an email or your screen: see Report Generation Options
- save a generated report immediately: see Saving Reports
- schedule automatic report generation: see Scheduling Reports
Resource Cold Spot Report
The Resource Cold Spot report is a key checkpoint report that provides resource utilization less than the specified metrics, or rather the inverse of the Resource Hot Spot report.
The Resource Cold Spot report helps you answer the following types of questions:
- Which servers and network devices in my infrastructure were the bottom consumers in various resource usage categories?
- Which servers have unused memory, or are under worked?
- Are all network devices correctly configured?
The resource consumer summaries rank physical and virtual servers as well as network devices in various resource-related categories, allowing you to correlate bottom-ranking consumers across categories to identify availability.
The report is also a valuable investigative tool that helps you quickly focus on the parts of your infrastructure that require troubleshooting. The report can be configured to include full listings of servers and network devices based on key resource-usage metrics such as memory and CPU usage, port throughput caps, or packet-issue counts. The high, low, and average for these metrics are presented, along with historical graphs for offending metrics.
The Resource Cold Spot report is a default report that is automatically created and saved for weekly generation on new Uptime Infrastructure Monitor installations, beginning the third day after Uptime Infrastructure Monitor was first installed. |
Resource Cold Spot Report Details
The following information comprises the Resource Cold Spot report:
| Servers | |
|---|---|
| Bottom Servers | Of the servers included in the report, the bottom five resource-consuming servers in terms of CPU and memory. These servers are listed regardless of whether they violated resource usage thresholds set during report configuration; if your entire infrastructure is meeting your resource usage criteria for the report, the bottom-five servers are still included in the summary for each category. |
| CPU | The percentage of CPU capacity used during the defined time period. In the Bottom Servers summary, this is an average value for the time period. |
| Mem | The percentage of memory used by processes for the defined time period. In the Bottom Servers summary, this is an average value for the time period. |
| Servers with Low CPU Usage | A listing of all servers included in the report whose average CPU usage for the time period was less than the threshold defined during report configuration. Each server's entry includes the following information to help correlate the metric with other metrics or events:
|
| Servers with Low Memory Usage | A listing of all servers included in the report whose average memory usage for the time period was less than the threshold defined during report configuration. Each server's entry includes the following information to help correlate the metric with other metrics or events:
|
| Network Devices | |
| Bottom Network Devices | Of the network-device type Elements included in the report, the five least inefficient network devices in terms of in rate, out rate, error count, and discards. These network devices are listed regardless of whether they violated throughput or error thresholds set during report configuration; if all of your network devices are passing the criteria for the report, the bottom-five network devices are still included in the summary for each category. |
| In Rate % | The percentage of the network device's maximum throughput, on a per port basis, that was used by inbound packets during the defined time period. |
| Out Rate % | The percentage of the network device's maximum throughput, on a per port basis, that was used by outbound packets during the defined time period. |
| Network Devices with Low In Rate | A listing of all network devices included in the report whose average in-rate percentage for the time period was less than the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the metric with other metrics or events:
|
| Network Devices with Low Out Rate | A listing of all network devices included in the report whose average out-rate percentage for the time period was less than the threshold defined during report configuration. Each network device's entry includes the following information to help correlate the metric with other metrics or events:
|
Creating a Resource Cold Spot Report
To create a Resource Cold Spot report, do the following:
- On the Reports tab, click Resource Cold Spot, which is found in the Performance and Analysis section of the reports tree panel.
- In the date and time range section, select a reporting window.
For more information, see Understanding Dates and Times. - In the Report Options section, configure which components comprise your report:
- bottom-five lists for servers or network devices in various resource-usage categories
- comprehensive lists of Elements that are experiencing performance issues in various resource-usage categories
- for the Element list, the threshold used to determine which are experiencing performance issues
- Determine which Elements are included in the resource cold-spot assessment by selecting Infrastructure Groups, Element Views, or individual Elements from the following sections:
- List of Groups
- List of Views
- List of Elements
- Continue with the desired report generation process:
- generate a report immediately to an email or your screen: see Report Generation Options
- save a generated report immediately: see Saving Reports
- schedule automatic report generation: see Scheduling Reports
Multi-System CPU Report
The Multi-System CPU report charts and compares the CPU performance statistics from multiple systems in your environment. These statistics indicate whether the systems are exhibiting balanced behavior, or if processes are forced off CPUs in certain circumstances.
Creating a Multi-System CPU Report
To create a Multi-System CPU report, do the following:
- In the Reports Tree panel, click Multi-System CPU.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- If you want the report to only include data from certain hours during the day, select those hours from the dropdown lists in the Daily Hours section.
For example, if you want to report to cover the hours from 1:00 a.m. to 1:00 p.m., select 1:00 from the Start dropdown list, and 13:00 from the End dropdown list. - If you want to generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems in your environment, select them from the List of Systems.
- Select a report generation option. See Report Generation Options for details.
- To save the report or schedule it to run at a specific time or interval, complete the settings in the Save Reports section of the subpanel.
See Saving Reports and Scheduling Reports for more information.
CPU Utilization Summary Report
The CPU Utilization Summary report generates a tabular summary of the CPU and memory consumption over a specific time period. Specifically, this report returns the following information:
- number of CPUs on the server.
- the total processor speed of all the CPUs, in MHz
- the maximum, minimum, and average CPU use, expressed as a percentage
- the maximum, minimum, and average memory use, expressed as a percentage
- the maximum, minimum, and average page scan per second, expressed as a percentage
Creating a CPU Utilization Summary Report
To create a CPU Utilization Summary report, do the following:
- In the Reports Tree panel, click CPU Utilization Summary.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- Select one of the following options from the Sort by dropdown list to sort the results that Uptime Infrastructure Monitor returns:
- Average CPU (the default)
- Hostname
- # of CPUs
- CPU Speed
- Maximum CPU
- Minimum CPU
- Average Memory
- Maximum Memory
- Minimum Memory
- Average Page Scan
- Maximum Page Scan
- Minimum Page Scan
- Select Ascending or Descending from the Sort Direction dropdown list.
- Optionally, in the Minimum sort value for inclusion field enter a value for the sort threshold.
The report displays items from the Sort By list, whose value is equal to or greater than the value in this field. For example, if you chose # of CPUs from the Sort by list and set this field to 2, the report only displays systems with two or more CPUs. - Select one or more of the following CPU statistics at which the report looks:
- sys
The percentage of CPU time that is used to carry out system processes. - usr
The percentage of CPU time that is used to carry out user processes. - wio
The percentage of CPU time that could be handling processes, but which is waiting for I/O operations to complete.
- sys
- Select one or more of the following statistics on which to report:
- CPU
The percentage of CPU resources that are used. - Memory
The percentage of system memory that is used. Page Scans
The number of page scans per second.The statistic you select must match the sort criteria that you selected in step 4. For example, if your sort criteria is Average CPU you must also select the CPU statistic. Otherwise, an error message appears when you try to generate the report. Optionally, in the Architectures to exclude field enter either the name of a system architecture or a regular expression that Uptime Infrastructure Monitor uses to ignore certain system architectures when generating the report.
For example, if you want to exclude all Solaris systems from the report, enter SunOS in the field.Uptime Infrastructure Monitor determines the architecture of a system by checking the output of the uname -a command on UNIX or Linux, or by analyzing one or both of the following Windows registry keys:
HKEY_LOCAL_MACHINE\\Software\\Microsoft\\ WindowsNT\\CurrentVersion
HKEY_LOCAL_MACHINE\\Software\\Microsoft\\ Windows\\CurrentVersion
- If you want to generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems in your environment, select them from the List of Systems.
- Select a report generation option. See Report Generation Options for details.
- To save the report or schedule it to run at a specific time or interval, complete the settings in the Save Reports section of the subpanel.
See Saving Reports and Scheduling Reports for more information.
CPU Utilization Ratio Report
The CPU Utilization Ratio report charts, in a table, the ratio of the percentage of CPU usage over a specified period of time. The ratio is derived by dividing the percentage of system time that is used by the percentage of user time. For example, if the amount of system time that is used is 22.12% and the amount of user time is 5.2%, then the CPU utilization ratio is 4.25.
This report contains the following information:
- the names of the hosts for which the report is generated
- the percentage of CPU time that is used to carry out user processes ( USR % )
- the percentage of CPU time that is use to carry out system processes ( SYS % )
- the CPU utilization ratio for each host, which is derived by dividing SYS % by USR %=
Creating a CPU Utilization Ratio Report
To generate a CPU Utilization Ratio report, do the following:
- In the Reports Tree panel, click CPU Utilization Ratio.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- If you want the report to only include data from certain hours during the day, select those hours from the dropdown lists in the Daily Hours section.
For example, if you want to report to cover the hours from 1:00 a.m. to 1:00 p.m., select 1:00 from the Start dropdown list, and 13:00 from the End dropdown list. - Optionally, enter a value in the Highlight ratios over threshold field.
Any ratios that exceed the value in this field are highlighted in the report. For example, if you enter 2 and a server returns a ratio of 3.5%, that ratio is highlighted. - If you want to generate reports for groups of systems, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems in your environment, select them from the List of Systems.
- Select a report generation option. See Report Generation Options for details.
- To save the report or schedule it to run at a specific time or interval, complete the settings in the Save Reports section of the subpanel.
See Saving Reports and Scheduling Reports for more information.
Wait I/O Report
The Wait I/O report enables you to determine the amount of time that processes spend waiting on I/O from a system device.
The Wait I/O report contains the following information:
- the names of the hosts for which the report is generated
- the average, maximum, and minimum wait I/O times expressed as percentages
Creating a Wait I/O Report
To create a Wait I/O report, do the following:
- In the Reports Tree panel, click Wait I/O.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- If you want the report to only include data from certain hours during the day, select those hours from the dropdown lists in the Daily Hours section.
For example, if you want to report to cover the hours from 1:00 a.m. to 1:00 p.m., select 1:00 from the Start dropdown list, and 13:00 from the End dropdown list. - Optionally, enter a value in the Highlight average WIO over threshold field.
Any system with an average Wait I/O percentage that exceeds the value that you enter in this field is highlighted in red in the report. As well, the following text appears in the header of the report:
Systems with an Average Wait I/O over x.x% are highlighted
Where x.x is the percentage that you entered in this field. - If you want to generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems in your environment, select them from the List of Systems.
- Select a report generation option.See Report Generation Options for details.
- Do one of the following:
- Click the Generate Report button.
- Enter a name for the report in the Save to My Portal As field, and optionally enter text in the Report Description field. Then, click Save Report.
The report parameters are saved to the My Portal panel. Doing this does not generate the report.
- To schedule the saved report to run at a specific time or interval, click the Scheduled checkbox.
See Scheduling Reports for more information on configuring a scheduled report.
Inventory Report
The Inventory report provides details about the composition of your monitored infrastructure by operating system, across physical and virtual Elements. The report contents can optionally be organized by group, and can include individual Element entries.
These different reporting options allow you to confidently assess your inventory from a variety of perspectives, and help you answer the following types of questions:
- How many older versions of the Uptime Infrastructure Monitor Agent are deployed on my systems?
- What is the operating system breakdown across my infrastructure, both virtualized, and on physical systems?
- I need to upgrade a particular OS version; which systems are candidates for this deployment?
Inventory Report Information
Because the Inventory report displays all monitored Elements, the report is intended for system administrators. Non-administrative Uptime Infrastructure Monitor users who do not have permission to view all Elements cannot view complete inventory listings. |
The following information can be displayed in the Inventory Report when you select Show Operating System Summary:
Operating System Summary | ||
unique breakdown of physical and virtual Elements, with totals by OS, and component totals for OS versions | ||
Physical Elements | the total number of systems-type Elements (i.e., not network devices, Applications, and SLAs) this total includes virtual machines that are not managed by a VMware vCenter server Element (e.g., LPARs or VMware VMs manually added to Uptime Infrastructure Monitor, and not through vSync) | |
Virtual Elements | the total number of Elements running on VM instances (i.e., VM instances with their own UUID) | |
Operating System | the detected operating system, including VMware environments | |
Version | the detected operating system version; build version details are listed if available | |
Element Name | the Element’s host name | |
Architecture | the detected hardware platform type on which the Element’s CPUs are running | |
Agent Version | if applicable, the version of the Uptime Infrastructure Monitor Agent that is running on the Element | |
Added Date | the date the Element was added to Uptime Infrastructure Monitor monitored inventory | |
Group | the Element’s Infrastructure group name | |
The following information can be displayed in the Inventory Report when you select Show Element Type Summary:
Element Type Summary | ||
unique breakdown of physical and virtual Elements by type, with when the element was added, monitoring status, which group contains each element, and component totals for each Element type | ||
Agent Elements | contains Elements identified by Uptime Infrastructure Monitor as Agents | |
vSphere Elements | contains Elements identified by Uptime Infrastructure Monitor as vSpheres | |
| Virtual Machine Agentless Elements | contains Elements identified by Uptime Infrastructure Monitor as Agentless Virtual Machines | |
| VMware vCenter Server Elements | contains Elements identified by Uptime Infrastructure Monitor as VMware vCenter Servers | |
| Network Device Elements | contains Elements identified by Uptime Infrastructure Monitor as Network Devices | |
Element Name | the Element’s host name | |
OS Type | the detected operating system, including VMware environments | |
Added Date | the date the Element was added to Uptime Infrastructure Monitor monitored inventory | |
Monitored | whether the Element is monitored (True) or not monitored (False) | |
| Group | the Element’s Infrastructure group name | |
The following information can be displayed in the Inventory Report when you select Show Monitor Summary:
Monitor Summary | ||
unique breakdown of physical and virtual Elements by type, with element name, assigned Service Monitor, whether the Element is monitored and for what period of time, whether there are associated Alert and Action Profiles, and component totals for each Element Service Monitor | ||
Agent Elements | contains Elements identified by Uptime Infrastructure Monitor as Agents | |
vSphere Elements | contains Elements identified by Uptime Infrastructure Monitor as vSpheres | |
| Virtual Machine Agentless Elements | contains Elements identified by Uptime Infrastructure Monitor as Agentless Virtual Machines | |
| VMware vCenter Server Elements | contains Elements identified by Uptime Infrastructure Monitor as VMware vCenter Servers | |
| Network Device Elements | contains Elements identified by Uptime Infrastructure Monitor as Network Devices | |
Element Name | the Element’s host name | |
Service Monitor | the name of the service monitor assigned to this Element | |
Monitored | whether the Element is monitored (True) or not monitored (False) | |
whether notifications are issued for this Element's service monitor (Yes) or notifications are not issued (No) regardless of status or interval | ||
| Monitoring Period | the Element's service monitor time period at which Uptime Infrastructure Monitor sends alerts | |
| Alert Profile | whether the Element has an associated alert profile (Yes) or not (No) Alert Profiles are templates that tell Uptime Infrastructure Monitor how to react to various alerts that are generated by service checks. | |
| Action Profile | whether the Element has an associated action profile (Yes) or not (No) Action Profiles are templates that direct Uptime Infrastructure Monitor when it encounters a problem on a monitored system. | |
Creating an Inventory Report
To create an Inventory report, do the following:
- In the Reports Tree panel, click Inventory Report.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- Optionally select the Don’t List Individual Elements check box to restrict the report to inventory summaries.
- Optionally select the Group by Selected System Groups check box to organize the report by group.
- If you want to generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific Elements in your environment, select them from the List of Elements.
- Select a report generation option.See Report Generation Options for details.
- Do one of the following:
- Click the Generate Report button.
- Enter a name for the report in the Save to My Portal As field, and optionally enter text in the Report Description field. Then, click Save Report.
The report parameters are saved to the My Portal panel. Doing this does not generate the report.
- To schedule the saved report to run at a specific time or interval, click the Scheduled checkbox.
See Scheduling Reports for more information on configuring a scheduled report.
Service Monitor Metrics Report
You can configure the Uptime Infrastructure Monitor service monitors to retain data, which is saved to the Uptime Infrastructure Monitor DataStore for later use. The Service Monitor Metrics report visualizes the retained data in a line chart.
For example, if you have configured a service monitor to retain response time data then this report charts any changes in the response time (in milliseconds) that have occurred over the time period that you specified for the report.
Creating a Service Monitor Metrics report is a two-step process:
- enter the basic parameters for the report
- select the values for the retained on which you want to report
Creating Service Monitor Metrics Reports
To create a Service Monitor Metrics report, do the following:
- In the Reports Tree panel, click Service Monitor Metrics.
- In the Date and Time Range area, select the dates and times on which to report. For more information, see Understanding Dates and Times.
- If you want to generate reports for systems in specific groups, select the groups from the List of Groups area.
- To generate reports for one or more views, select the groups from the List of Views area.
See Working with Views for more information about views. - If you are generating reports for specific systems in your environment, select them from the List of Elements.
- Click Go to page 2.
A table containing the current retained service metrics appears in the Service Metrics subpanel. - Click the checkboxes in the Select column to select the variables on which you want to report.
- Optionally, select one of the following:
- Show all non-ranged metrics on one chart
This option combines all of the variables you selected in one chart. Any ranged metrics appear in their own charts. - Display charts as stacked area
Each chart in the report has two or more data series stacked on top of each other, rather than the line graph that usually appears in the report.
- Show all non-ranged metrics on one chart
- To save the report, do the following:
- Enter a name for the report in the Save to My Portal As field.
- Optionally, enter text in the Description field.
- Click Save Report.
The report parameters are saved to the My Portal panel. Doing this does not generate the report.
- To schedule the saved report to run at a specific time or interval, click the Scheduled checkbox.
See Saving Reports and Scheduling Reports for more information.